Bulletproof Enterprise Data Security Measures to Protect Your Remote Team
Protecting your remote team requires more than just a strong password or two. You need to be taking enterprise data security measures that will ensure all of your information is safe.
Businesses of all sizes across the world are facing a battle on two fronts: controlling the spread of COVID-19 in their workforce by shifting to work-from-home arrangements and combating the heightened threat of cybersecurity attacks.
Remote Working Could Expose You to Cybersecurity Vulnerabilities
Experts unanimously agree that the increase in cybersecurity threats is linked to the trend of remote working. According to Global Cyber Center (NYC) Senior Analyst William Altman, “Organisations of all kinds are facing an uptick in email-based threats, endpoint-security gaps and other problems as a result of the sudden switch to a fully remote work setup.”
FBI reports that instances of cybercrime jumped by as much as 300 percent since the beginning of the pandemic with its Internet Crime Complain Center (IC3) receiving between 3,000 and 4,000 cybersecurity complaints every day, a huge spike from the pre-COVID-19 average of 1,000 complaints per day.
In particular, your remote employees should watch out for these four signs of a possible cyber breach:
- New programs that were not installed appear (check your desktop icons or start window)
- Slowdown in device performance
- Unfamiliar pop-up windows appear
- Uncontrolled movement or loss of control of the mouse or keyboard
Learn More: Outsource Data and Information Security Teams
How to Quickly Develop a Bulletproof Enterprise Data Security Strategy
Speed is crucial in resolving your business’s cybersecurity challenges to protect your confidential data and ensure compliance, but it can be overwhelming where to start—especially if you’re still getting used to a remote working setup.
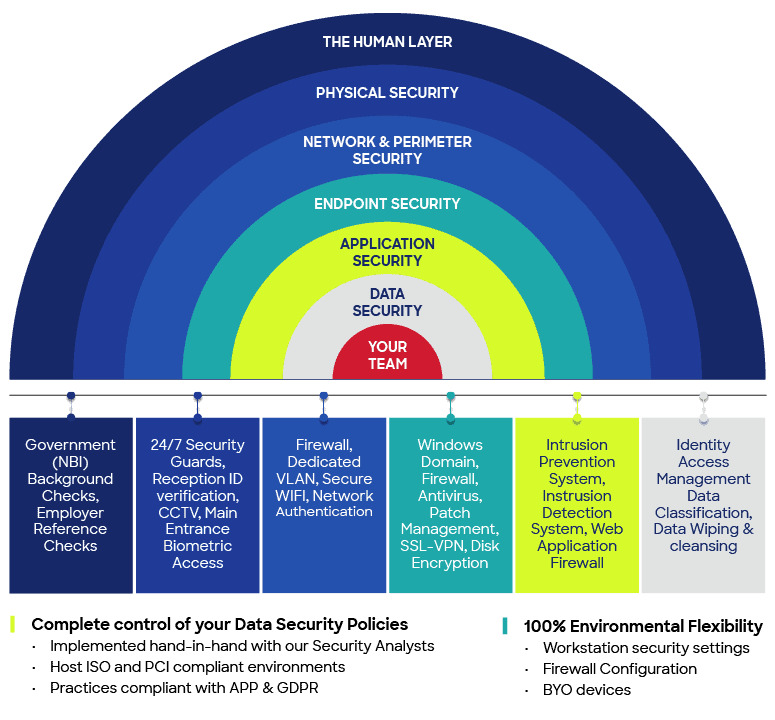
The Emapta IT Security team has adopted the best practices to improve our capabilities and consider key areas of data security measures to protect our client partners’ data while their staff transitioned to a remote setup. To help you develop a fully comprehensive enterprise data security strategy, we’re also sharing these tips that you can immediately implement for your remote teams:
1. Keep your IT security policy, procedure, and process updated
Exposing confidential data will not only lower consumer confidence in your firm but can also lead to costly penalties. Make sure to adhere to GDPR recommendations and improve policies to guide employees on how to keep business data protected and safe all the time.
Emapta IT and Security policies are a systematised mix of actionable procedures and technical specifications on Security Standards and Requirements, Acceptable Usage Policy, and Security Incident Response Procedures. All of which are built to provide proper and timely response to cyber-attacks, data breaches, and violation of company policies.
2. Constantly educate your staff about data security
Nowadays, it’s no exaggeration that damaging data breaches are only one click away. MIT reports that a large volume of successful cyberattacks is caused by human error, “including an estimated 90% of such attacks in the U.K. in 2019.”
A huge part of safeguarding your data is sharing and enforcing protocols and behaviors for secure remote working in your organisation. Once you’ve updated your cybersecurity policy, your data protection officer or IT security staff should conduct training sessions on the tools, processes, and best practices that your remote workforce should follow in your day-to-day operations. They should also be available and prepared to handle concerns from your remote staff (such as reporting a possible threat or clarifying a new authentication process).
Data security education (with reference to our IT Acceptable Usage Policy) is part of Emapta’s New Hire Induction for all employees. We also conduct IT Security Awareness Programs for remote staff who are handling Personally Identifiable Information (PII), Special Personal Information (SPI), financial records, or credit card information. Finally, we regularly conduct security awareness sessions with our client teams to ensure they are aware of the latest security standards and measures.
Everyone—from the leadership team down to your rank-and-file employees—should rally around the idea that data security is everyone’s responsibility, and be extra vigilant in every action they take—even if it’s something as simple as opening an email attachment or thinking and asking before clicking anonymous links.
3. Secure network connection and computing device
Regulating data access is crucial so only authorised users are granted access to view and manage sensitive data. Since your remote team members are using their personal network at home, they’re more vulnerable to cybersecurity threats than in the office. In this case, you need more than a device’s built-in firewall to fend off attacks. Deploy a corporate virtual private network (VPN) to encrypt your staff’s connection to your servers. A VPN provides an encrypted tunnel to help keep your data safe in transit and enables your employees to do their job in a secure environment.
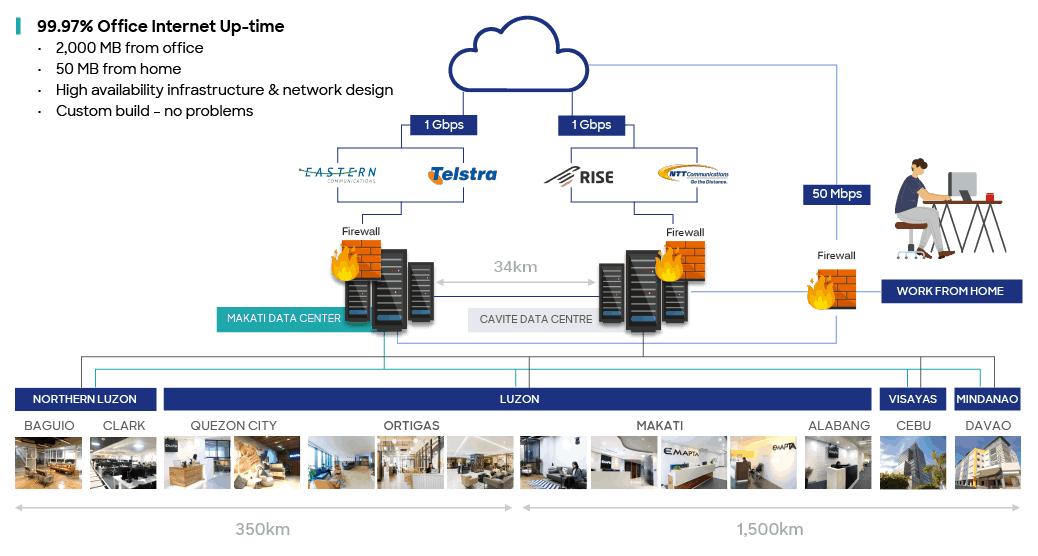
Being proactively conscious of cyber-threats, we provide financial-grade network security level to client partners and their remote teams through Emapta Office Connect, a custom-built VPN service that gives our client teams the confidence to safely collaborate anywhere they’re located. We have also installed a high availability perimeter firewall that protects our clients’ private network from external cyber threats. Each client is assigned their own dedicated, secure network segment that cannot be accessed by other Emapta tenants. Our standard operating environment is inclusive of centrally managed enterprise anti-virus, malware, ransomware, firewall enabled software configured for schedule system and security updates. Moreover, Emapta IT and Security management has provisioned PCI-DSS, HIPPA and GDPR-ready working environments.
Our data centres provide bank-level security to your remote staff:
Read More: Maximum Protection, Minimal Risk
4. Storage backup and recovery
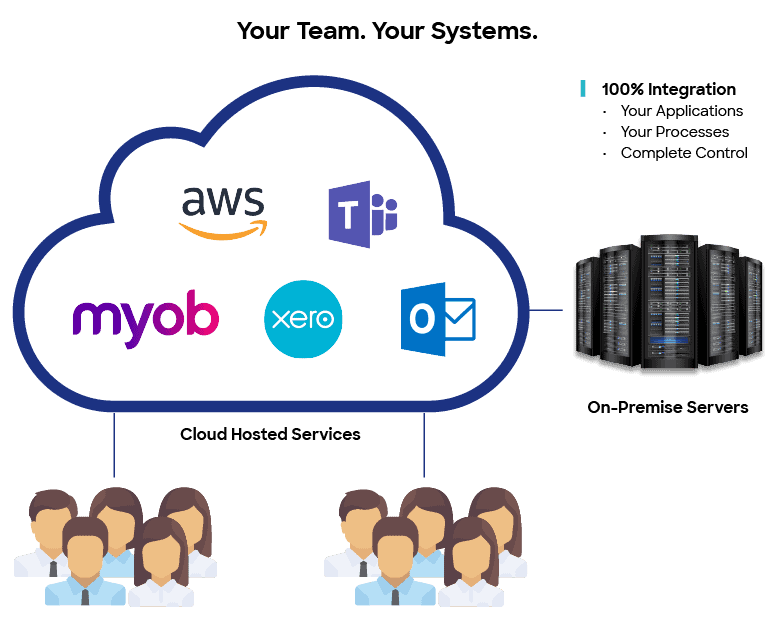
When it comes to safeguarding your data, invest not just in physical backup devices but also in cloud-based data storage solutions such as OneDrive, SharePoint, Google Drive, and Dropbox. When using a cloud-based backup system, you should control user access and always enable request-and-response protection mechanisms when sharing links to files or folders.
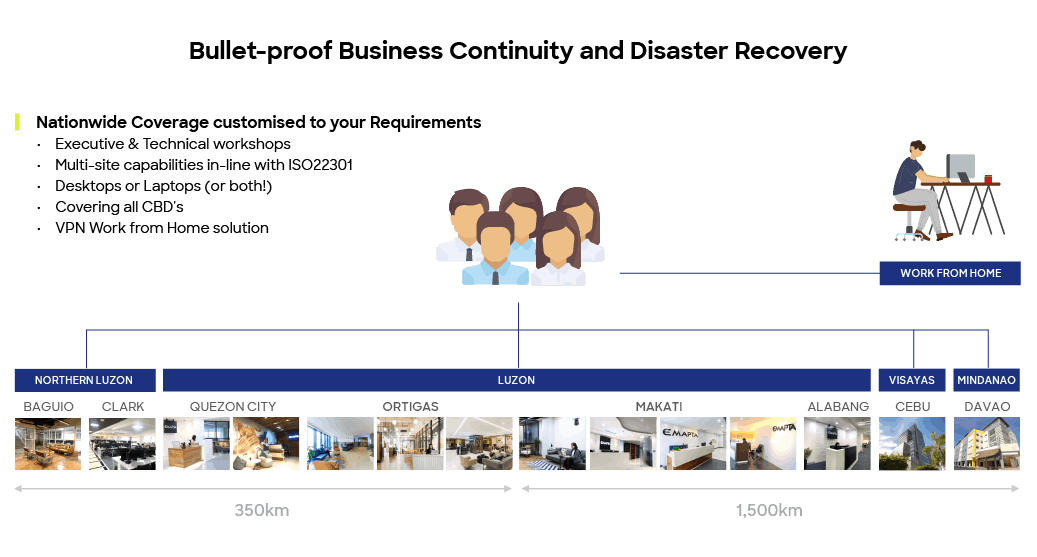
At Emapta, our IT security team encrypts storage media as part of our data security standards to lock down files and folders protect from them unauthorised access to be ready for the worst-case scenario: in case systems get hacked, irretrievable data loss is prevented with a backup. Regardless of our client’s size, we continuously deliver information security solutions suited to their specific needs—including data management and backup. Developed within the stringent Information Technology Infrastructure Library (ITIL) framework, our IT infrastructure is complete with full redundancy, automatic fail-over, and 24/7 IT Support Engineers inside our 14 offices—and extended over to each of our clients’ remote staff.
Our client partners can fully integrate their cloud-hosted services and on-premise servers into their staff’s remote setup:
5. Data encryption and access control
Your data should be protected at all times, whether it’s in transit (every time someone accesses it) and at rest (when it is in storage). In a remote setup, encryption and access control are the two dimensions of data protection.
Encrypting devices can be complicated if your employees are not using their work-supplied laptop or phone while working remotely. If you’re in a BYOD setup, your employees’ devices should be protected through encryption. Otherwise, there should be arrangements to ensure that they’re using only their work-supplied devices.
Part of our comprehensive enterprise data security approach is encrypting storage devices on-site and off-site essential to our endpoint security posture. In a setup where employees use their personal device when working, we require them to encrypt their storage drive since they’re handling sensitive company information. We also encrypt and encapsulate the data on transit in our logical network to protect the reputation and integrity of the data information.
Emapta-provided remote workstations are also joined to a Windows Domain and are enforced with security orientated policies:
- User permission restricted to standard access
- Only client employees can authenticate to client workstations
- USB storage devices are disabled
- User authentication attempts are logged
- Auto-locking of workstations after a period of inactivity
Key components of Emapta’s 8-layer physical and digital security approach:
6. Monitor your computing environment for potential service impact
Another way to block illegal access, aside from device encryption and access restriction, is to have a network security monitoring system that can help your IT security team detect any unusual activity or presence in your network as well monitoring your remote team’s web/application activity and bandwidth usage. You can also set up a remote control or desktop sharing software in your staff’s computer such as AnyDesk or TeamViewer for easy access in case of troubleshooting or for full transparency of your remote staff’s browser or application usage.
Our dedicated 24/7 network operations centre oversees all internal and client-related network activity. This helps client partners detect unusual events and mitigate potential service impact. Our network operations team also ensures that remote workers can access the resources they need to perform their day-to-day tasks. In case of any technical concerns, our Help Desk team quickly responds through remote desktop access and virtual support.
7. Make your business continuity plan (BCP) cybersecurity-ready
The degree to which technology is integrated into our business’ operations has significantly increased over the years. This is the best time to revisit your BCP and update it with data security and network backup measures for force majeure events. For instance, our BCP-ready IT infrastructure is equipped with Multiple ISP Connectivity—redundant ISP configuration using a combination of the five globally recognised internet service providers for load balancing, resilience and redundancy, and a logical network design which offers V-LAN segregation of our client partners, bank-level security protocols and multiple layers of redundancy for all core infrastructure.
Moreover, we can meet any demand anytime needed as our network is designed to be upgradable, expandable and flexible enough to change with our client partners’ needs and circumstances. Our IT security team also conducts regular penetration and BCP testing to ensure security controls are accessible in the event of component failure.
We offer business continuity solutions tailored to your remote work environment:
Keep your remote teams protected from security breaches.
Implement bulletproof ICT solutions today.
Remote work is here to stay—for now. And if you find work-from-home more optimal for your business, we’re capable of seamlessly transferring your team to a remote setup through Emapta Anywhere™, our secure work-from-home solution. Feel free to collaborate with the best talent from every corner of the country in a setup that is digitally secured in the same level as working from any of our 14 offices. Maximise your remote team’s potential as we minimise the cybersecurity risks through our enterprise-grade data security and data loss prevention protocols.
Putting the above tips into practice is already a huge step in protecting your virtual working environment, but you can also get help from our in-house IT experts to provide you with more a broad range of data security resources—ranging from a network operations centre to a data security software stack—for a holistic cybersecurity strategy that puts your mind at ease.